What is PKI? Definition & guide to Public Key Infrastructure
Public key infrastructure (PKI) manages identity and security within Internet communications to protect people, devices, and data. Learn more here from Sectigo®.
Organizations depend on PKI solutions to authenticate and encrypt information flowing through web servers, digital identities, connected devices, and applications. Establishing secure communications is paramount to ensuring business continuity and proactive risk management as organizations increasingly rely on the Internet for critical business systems.
PKI is an essential component of a Zero Trust architecture as described by the National Institute for Standards and Technology (NIST) where trust is never granted implicitly and must be continually evaluated.
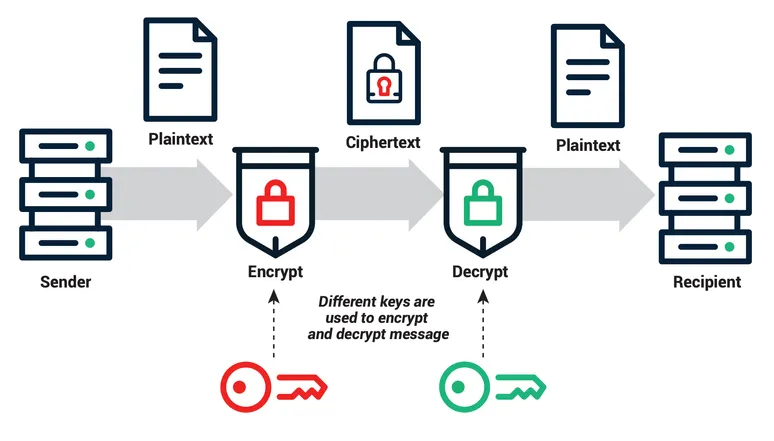
Public key cryptography is the core technology that enables PKI through two separate but related keys for encryption and decryption. The resulting key pair, a public key used to encrypt a message and an associated private key to decrypt it, is also referred to as asymmetric cryptography. The key pair uses cryptographic algorithms to guarantee that encrypted communications can only be decrypted by the intended recipient, the holder of the secret key.
How PKI based certificates provide secure digital identity
The International Telecommunications Union (ITU) X.509 standard defines the format of PKI-based certificates. Unobtrusive and ubiquitous, users encounter digital certificates every day when using websites, mobile apps, online documents, and connected devices. In general, the term digital certificate describes all X.509 certificates. It’s a list that includes SSL/TLS certificates, email signing certificates, code signing certificates, and document signing certificates.
Often referred to as "online credentials," a digital certificate:
- Validates the identity of the owner.
- Provides the owner's encrypted public key.
- Is issued by a trusted Certificate Authority (CA) that verifies authenticity.
As discussed earlier, public keys are created using a complex asymmetric algorithm to pair them with an associated private key. In public key cryptography, an encryption key (which could be the public or private key) is used to encrypt a plain text message and convert it into an encoded format known as ciphertext. Then, the other key is used as a decryption key to decrypt the ciphertext so that the recipient can read the original message. This all happens automatically and is invisible to the user.
As the public key is published for all the world to see, more are created using a complex cryptographic algorithm to pair them with an associated private key by generating random numeric combinations of varying length so that they cannot be exploited through a brute force attack. Unlike the publicly accessible key, the private key is a secret key known only by its owner. Private keys are generated using the same algorithms that create public keys to create strong key pairs that are bonded mathematically.
The most common cryptographic algorithms used to generate keys are:
- Rivest–Shamir–Adleman (RSA)
- Elliptic curve cryptography (ECC)
- Digital signature algorithm (DSA)
These algorithms use various computation methods to generate random numeric combinations of varying lengths. The key size or bit length helps determine the strength of protection. Standards organizations like the CA/Browser Forum define baseline requirements for supported key sizes. For example, common uses of 2048-bit RSA keys include SSL certificates, digital signatures, code signing certificates, and other digital certificates. This key length offers sufficient cryptographic strength to keep hackers from cracking the algorithm.
Why not use two secret keys instead of one public key and one private key? While it may seem counterintuitive, using a key pair consisting of two private keys for encrypting and decrypting sensitive information, a process called symmetric key algorithm, is not more secure than asymmetric encryption. In addition, using symmetric key algorithms requires that both parties in the communication have access to the secret keys, increasing the risk as both now need to keep the secret. Finally, these types of algorithms cannot easily scale as it is nearly impossible to coordinate the vast number of connections necessary to privately share all combinations of private keys.
The benefits of PKI
Cryptographic keys provide a validation mechanism that protects identities and data from unauthorized access or use. They are an essential part of an enterprise cybersecurity program to protect websites, e-commerce transactions, documents, emails, servers, and other assets against attacks from cybercriminals.
PKI provides scalable data and digital identity security that can secure billions of messages exchanged daily by organizations over their own networks and across the Internet. What enables this scalability is that public keys can be distributed widely and openly without malicious actors being able to discover the private key required to decrypt the message. In addition, PKI has evolved to become even more versatile, delivering interoperability, high uptime, and governance.
At its core, PKI enables confidentiality by allowing two communicating parties to send and receive sensitive data privately. The organizational benefits are extensive and measurable, delivering secure communications that:
- Protect customers.
- Safeguard enterprise intellectual property.
- Strengthen compliance programs.
- Prevent data breaches.
- Support a growing remote, distributed workforce.
- Secure an increasing number of cloud applications and Internet of Things (IoT) devices.
In essence, it is the best protection for the digital identities of your people, devices, and data, allowing individuals, organizations, and even devices to establish trust in the digital world.
Common PKI applications
There are many applications of PKI technology, including Web server security, digital signatures and document signing, and digital identities.
Web server security
Public key cryptography is the basis for the secure sockets layer (SSL) and transport layer security (TLS) protocols that are the foundation of HTTPS secure web browser connections. SSL/TLS certificates encrypt Internet communications and ensure a trusted client-server connection. Without them, cybercriminals could exploit the Internet or other IP networks using a variety of attack vectors to intercept messages and access their contents.
Digital signatures and document signing
In addition to being used to encrypt messages, key pairs can be used for digital signatures and document signing. PKI uses the sender's private key to verify their digital identity. This cryptographic verification mathematically binds the signature to the original message to ensure that it has not been altered.
Code signing
Code Signing enables application developers to add a layer of assurance by digitally signing applications, drivers, and software programs so that end users can verify that a third party has not altered or compromised the code they receive. To verify the code is safe and trusted, these digital certificates ensure the integrity of containers, the code that they run, and the production applications that use them.
Email certificates
S/MIME certificates validate email senders and encrypt email contents to protect against increasingly sophisticated social engineering and spear-phishing attacks. By encrypting/decrypting email messages and attachments and by verifying identity, S/MIME email certificates assure users that emails are authentic and unmodified.
SSH keys
SSH keys are a form of X.509 certificate that provides a secure access credential used in the Secure Shell (SSH) protocol. The SSH protocol is widely used for communication in cloud services, network environments, file transfer tools, and configuration management tools.
SSH keys authenticate identity and protect those services from unintended use or malicious attacks. SSH keys not only improve security, but also enable the automation of connected processes, single sign-on (SSO), and identity and access management at the scale that today's organizations require.
Digital identities
Digital identity authentication is a critical element of a Zero Trust strategy to authenticate people, data, or applications. Securing identities with X.509 digital certificates is more important than ever as data and applications expand beyond traditional networks to mobile devices, public clouds, private clouds, and IoT devices. Digital identity certificates based on this standard enable organizations to improve security by replacing passwords, which attackers have become increasingly adept at stealing.
Establishing trust: The role of certificate authorities in PKI
A critical component of deploying X.509 certificates is a trusted Certificate Authority (CA) or agent to issue certificates and publish the public keys associated with individuals' private keys. Without this trusted CA, it would be impossible for senders to know they are in fact using the correct public key associated with the recipient's private key, and not the key associated with a malicious actor intending to intercept sensitive information and use it for nefarious purposes.
Trusted third-party organizations, like Sectigo, act as certification authorities, but many enterprises and technology providers also choose to act as their own in-house CA. They may also decide to use self-signed certificates.
Regardless of the deployment approach, the CA must be trusted to:
- Check and vouch for the identity of all senders for whose public keys they publish.
- Ensure that those public keys are indeed associated with the private keys of the senders.
- Safeguard the levels of information security within their own organization to guard against malicious attacks.
The value of PKI automation and certificate management
Certificate management may be perceived as a simple, day-to-day task for an IT or web administrator, but ensuring certificates are individually valid is time-consuming and costly. For example, even a minimal, manual SSL certificate issuance with a single web server and domain instance involves multiple steps. The task can easily take a couple of hours, with labor costs adding up to over $50 per web server.
Now, multiply that effort across the thousands or millions of PKI certificates across all the networked devices and user identities in a global organization. Finally, add in the labor required to perform lifecycle certificate management to incorporate processes for discovery, installation, monitoring, and renewal.
The result of manual certificate management is a costly, time-consuming, and technically demanding challenge for busy IT teams. More vitally, a manual approach can expose organizations to sudden outages or failure of critical business systems along with breaches and attacks from cybercriminals.
Automating the end-to-end process of certificate issuance, configuration, and deployment delivers a clear return on investment (ROI) for CIOs and CSOs seeking to reduce risk, meet regulatory compliance requirements, control operational costs, and launch services to market faster.
Today’s PKI solutions provide functionality that improves administration and lifecycle certificate management through:
- Automation: Completing individual tasks while minimizing manual processes.
- Coordination: Using automation to manage a broad portfolio of tasks.
- Scalability: Managing certificates numbering in the hundreds, thousands, or even millions.
- Crypto-agility: Updating cryptographic strength and revoking and replacing at-risk certificates with quantum-safe certificates very quickly in response to new or changing threats.
- Visibility: Viewing certificate status with a single pane of glass across all use cases.
Save time and maintain control with Sectigo PKI automation
Given the disparate systems, applications, and devices that use digital certificates, IT teams often manage distinct automation services from many different vendors. Running multiple automation platforms means they are often not as efficient as they could be.
Sectigo provides certificate automation solutions that allow enterprises to be agile and efficient while maintaining control of all the certificates in their environment. Sectigo supports automated installation, revocation, and renewal of SSL/TLS and non-SSL certificates via industry-leading protocols, APIs, and third-party integrations.
A single certificate management dashboard that automates discovery, deployment, and lifecycle management across all use cases and vendor platforms can deliver the efficiency that automation promises. Moreover, with Sectigo, you will never run into a certificate volume cap, as you might with open source alternatives. Sectigo’s automation solutions enable your security team to easily enforce cryptographic security policy; protect communications; prevent data loss via unauthorized access; and future-proof systems, applications, and devices across the enterprise.
Learn more about how automated digital identity management is a fundamental element in Zero Trust security architecture, and explore Sectigo’s certificate management solution for enterprises.
And as working from home becomes the standard, businesses must secure every user, device, and application identity. Download our e-book to learn the 4 actions IT can take to ensure business continuity using identity management automation.