Prevent DDoS attacks with proper cybersecurity
DDoS (Distributed Denial-of-Service) attacks disrupt websites by flooding servers with traffic, causing downtime and potential financial losses. These attacks leverage botnets to overwhelm infrastructure and target vulnerabilities. Preventative measures, including system updates, robust monitoring, firewalls, and specialized services like SiteLock, are crucial to mitigate risks and protect your business.
You may have heard the term “DDoS attack” mentioned in online circles, especially when talking about website security, but what is it exactly? A DDoS, or distributed denial-of-service, attack is an attempt by a cybercriminal to flood a server with traffic to overwhelm its infrastructure. This causes a site to slow to a crawl or even crash so legitimate traffic won’t be able to reach the site. This type of attack can do a lot of damage to your online business.
These cyberattacks can run a wide range of purposes, from annoyance and “hacktivism” to massive loss of business. What makes these unique compared to other forms of hacking is the motivation. While other forms of malware, like ransomware and scareware, are attempts to siphon money from a victim, DDoS attacks are purely designed for chaos and disruption.
The amount of downtime and damage they can cause is why they are talked about so often. Hackers employ DDoS attacks regularly, and you need to be on the lookout for them so they do not impact you too severely.
How does a DDoS attack work?
Most DDoS attacks are done with botnets – groups of computers all acting together. These computers will all attempt to access a website simultaneously, overwhelming the server and bringing it down.
How do they get these botnets? By hijacking other machines. Often, a hacker will use malware or take advantage of an unpatched vulnerability on someone else’s server to gain access to it via Command and Control (C2) software. By leveraging these exploits, hackers are able to amass large numbers of computers in a relatively cheap and easy way, which they can then deploy for their own nefarious purposes.
Once they have control over enough machines, the hackers can then issue a command to the entire botnet, which then attempts to access the target server. When too many computers are trying to access a server all at once, service outages are common. The end result is an interruption in service and lost productivity.
This can be anything from a childish prank to revenge against a business. And while it sounds harmless at first, it’s important to know that the average cost of a DDoS attack to even small business operations can be as much as $120,000 – enough to bring many small businesses to their knees. Large corporations can lose millions.
An analogy to illustrate
Picture a two-lane highway. It’s strong, safe, reliable, and you drive on it every day without any issues because it serves its purpose. The city put that highway there because they have a reasonable estimate of how many cars are going to drive on it during the day.
Now, imagine a sudden event that leads to thousands of cars trying to use that road at once. You try to get onto the onramp, but when you reach the highway, you can’t get on. The road is completely clogged with traffic, and now you’re going to be late to your destination - if you arrive at all.
That is, essentially, what a DDoS attack is.
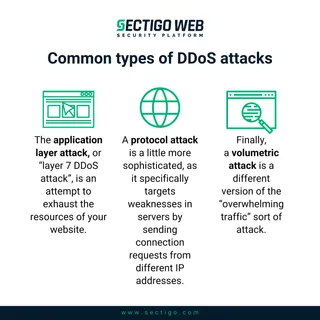
Common types of DDoS attacks
These attacks take many forms and they continue to evolve. Often, without the right monitoring system in place, you could be a victim of a silent attack without your knowledge - and by the time you realize it, your business has already ground to a halt. The most common types include:
- The application layer attack, or “layer 7 DDoS attack”, is an attempt to exhaust the resources of your website and consume all of its available bandwidth. When a hacker sends a lot of traffic from many different computers suddenly to a site, the server gets overwhelmed very quickly. Repeatedly, the traffic sends reload requests to the server (like hitting “refresh” on your browser). Eventually, the server throws back errors because it can’t handle the workload anymore.
- A protocol attack is a little more sophisticated, as it specifically targets weaknesses in servers by sending connection requests from different IP addresses. This doesn’t require a large system of computers. Each connection request needs a response, and the server gets overloaded rather quickly as its resources are exhausted.
- Finally, a volumetric attack is a different version of the “overwhelming traffic” sort of attack. In this case, the bots are sending data to the server and expecting a response. Do this enough times, and the response becomes too long. This data is artificially amplified before sending to the server, which exhausts resources quickly as it tries to handle the influx.
Depending on the DDoS attack type, they can be difficult to defend against without the latest detection and mitigation tools at your disposal.
How to prevent a DDoS attack
If you find yourself already in the midst of a DDoS attack, time is of the essence. Continuous monitoring is a major component, and you want a reliable alert system in place that will provide real-time notifications. If a DDoS attack begins on your server, you need to be able to catch it early and act quickly. If you can act quickly enough, you hopefully won’t see much effect on your normal users. You can block IP addresses with your firewall and keep them from gaining access to your server. You might even be able to isolate the targeted system and close inbound traffic to it.
If an attack hasn’t happened on your website yet and you are just looking to prevent this incredibly common type of attack, consider the following.
Develop a response plan
It may sound silly to say that prevention starts with a response plan, since that implies you didn’t prevent the attack.
But before you do anything else, you need to have a step-by-step plan in place. You can’t respond to a DDoS attack on the fly. It takes preparation and planning in advance with the end goal of preventing unnecessary damage to your business.
- Check your systems. All of them. Every asset you have online could be targeted. Make a checklist of every system that could be vulnerable to a DDoS attack. When you are hit, you can then run through the list and see if you can isolate and save systems that haven’t been affected yet.
- Create a response team and give them clear tasks. An attack is not the time to be debating and delegating. That should have been done already. Make sure everyone’s roles are clear.
- Make a list of emergency communications. It’s also crucial to understand who needs to know what and when. Your customers, your service provider, and any other security vendors need to know what’s going on so that they can each respond accordingly.
Now, that’s for after an attack. What can you do right now to prepare and prevent the attack from hitting you at all?
Keep your system updated
This step is crucial - for DDoS mitigation but also in all matters of online security. It does you no good to try to mitigate any risk to your system if you fail to keep it updated. Timely updates will address vulnerabilities in your system, close holes that hackers could get into, and mitigate as much risk as possible right out of the gate.
If your website runs on Wordpress, go to the updates page and make sure everything has been updated recently. Get rid of plugins that are outdated and no longer being developed. You don’t want to take any chances.
You can close off more holes to your potential attackers by taking this step than by almost anything else you do. And fortunately, even those who aren’t the most tech-savvy can handle it. Most updates are automated and able to be started with one click.
When your infrastructure is updated, you can effectively minimize the threat of attack.
Practice basic online security
Nothing fancy or complicated here – strong passwords (and updating them on a regular basis) and secure firewalls will do wonders for your protection.
Get proper DDoS monitoring
Thanks to cloud-based service providers, it has never been easier or more affordable to put a service in place that can keep an eye on your system and protect it from potential DDoS attacks.
SiteLock, a Sectigo company, offers complete website security plans that automatically scan, detect and shutdown attack attempts before they develop into something more sinister – and more damaging. For example, one feature of SiteLock is that it connects your site with a global content delivery network (CDN) that not only speeds up your site but also adds layers of DDoS protection. Other features include Web Application Firewall (WAF), malware removal, and backup services.
All of these tools add layers of protection between the incoming web traffic and your server, and they inspect the traffic as it comes in to analyze and detect DDoS attacks. Once detected, the attacking traffic can be isolated and dealt with - without disrupting the functionality of your site.
Having the right tools in place can prevent you from being a victim. Protect your business with one of SiteLock’s security plans today. And to ensure your enterprise’s communications are secure, learn about Sectigo’s automated digital certificate management solution.