First U.S. IoT Security Law Signed in California – Here’s What It Means


At the end of September 2018, the Governor of California signed country's first Internet of Things (IoT) security law, calling for reasonable security features. This is the first cybersecurity bill governing IoT devices, making California the first state in the country to establish formal legislation.

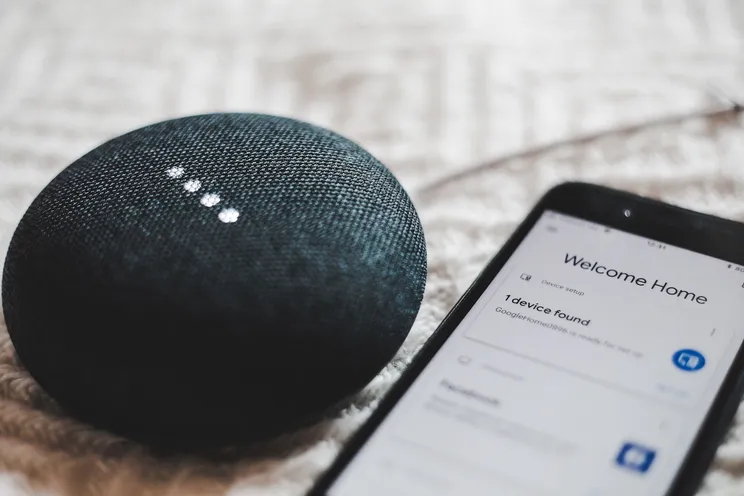
At the end of September 2018, the Governor of California signed country's first Internet of Things (IoT) security law, calling for reasonable security features. This is the first cybersecurity bill governing IoT devices, making California the first state in the country to establish formal legislation. The news is quite timely given that earlier this year the FBI issued a warning about threat actors actively searching for, and compromising, vulnerable IoT devices to route cyberattacks.
The bill, SB 327 (Information Privacy: Connected Devices), mandates that any manufacturer of IoT or smart devices ensure that the appliance has “reasonable” security features that “protect the device and any information contained therein from unauthorized access, destruction, use, modification, or disclosure.”
We are not surprised to see government intervention in Internet of Things (IoT) security, especially since the stakes are so high for privacy and safety. However, anyone reading the bill will find the wording to be open-ended and vague. A section of the bill specifies that default passwords must be unique to each device. This is an obvious reference to the Mirai Botnet, but the bill does not call for other safeguards like ensuring strong authentication based on digital identities.
Since the government is not in a position to prescribe specific technologies that could potentially be quickly outdated, this bill creates opportunities for companies to define and quickly bring to market next-generation security and authentication tools. For example, the removal and disabling of open ports like telnet or FTP, which would have its own authentication.
All IoT device manufacturers and consumers should read and educate themselves about SB 327. Here are some precautions for IoT vendors to consider before January 1, 2020, when the law goes into effect:
- Leave security to the experts and work with a proven security partner you trust
- Stop using static credentials for authentication like username and password and weak symmetric tokens
- Leverage strong authentication based on digital identities that are renewed (not static) and difficult to steal; this should increase trust and confidence within the supply chain and across the entire ecosystem including vendors and customers
With just over a year to go until the law goes into effect, our team will continue to innovate and develop the framework for IoT vendors to further increase the level of security they deliver to their customers. We will also be interested to see how other states react to this new California law and if other states will draw up similar legislature.
If you have any questions regarding how this law might affect your company, please contact [email protected].