Automated S/MIME Pays for Itself by Eliminating Common Support Issues
While automated certificate management is not a requirement of S/MIME, it is a feature that is highly recommended. Enabling employees to share the burden of managing certificates may save a small amount of money in the short run, but problems will almost certainly arrive in the long run.
Businesses across every industry depend upon email as an indispensable method of communication, helping customers, clients, employees, partners, vendors, and more interact. With private and confidential information being communicated over email every day, it should come as little surprise that email encryption tools like S/MIME have become an important part of organizational security.
Using encryption and digital signatures remains the best way to ensure the integrity and privacy of email communications. Tools like S/MIME allow the user to verify that the email really came from the supposed sender, to detect whether the content of the email—or any attachments within—has been changed in any way, and to proceed with the confidence that no one other than its intended recipient could have read the email.
These features represent important weapons in the fight against business email compromise (BEC) fraud. Digital certificates also play a critical role in helping organizations comply with regulatory requirements worldwide, such as the strict GDPR requirements that organizations operating in Europe must meet. S/MIME presents an elegant solution: using S/MIME for this type of encryption allows both the sender and recipient to utilize their existing S/MIME-capable email applications, while other solutions would likely require a new, separate email application or the use of a cumbersome web portal which requires the recipient to perform the risky operation to click on a link in an email. S/MIME represents email security made easy. S/MIME ensures the email is encrypted on the sender and recipient mail servers; an important layer of defense, especially when the mail server is in the cloud.
The Costs of NOT Automating Deployment
While automated certificate management is not a requirement of S/MIME, it is a feature that is highly recommended. Enabling employees to share the burden of managing certificates may save a small amount of money in the short run, but problems will almost certainly arrive in the long run. One Sectigo customer described the experience of forgoing automatic certificate management:
“We deployed the secure email certificate for our end users four months ago and [were] faced with the difficulty of deployment. Although we created a step-by-step guide for end users to download and install their own certificate, a lot of support requests were received to accomplish the setup.”
The difficulty associated with manual certificate management led this customer to seek out an easier solution from Sectigo, eventually incorporating automatic certificate management and installation into their solution. In most cases, setting up this automation costs less than a single support call—and saves the valuable time of employees no longer forced to manually manage their S/MIME certificates.
The expense of lost employee productivity is also notable. For instance, if a junior attorney at a law firm (who charges clients $240/hour) spends at least a half hour of billable time struggling to install a digital certificate on her iPhone, and support (paid $100/hour) takes the same amount of time to troubleshoot an incomplete or confused install, the firm has spent $170 simply to deploy one digital certificate—more than 5x the cost of a S/MIME certificate that could have automatically been provisioned to the user.
Preventing Painful Problems
Without automation, the risk of exposure due to human error skyrockets. How does automation help? Here are some of the most common problems caused by manual certificate management, most (if not all) of which can be addressed with effective automation:
- Failure to publish a new certificate. Failure to publish a new certificate to the corporate global address list means that senders from Outlook and ActiveSync mobile mail applications cannot find the certificate required to encrypt for the recipient. The employee will either spend a great deal of time figuring out how to publish their certificate, or the senders will not use encryption.
- Failure to utilize Global Address List. When the Global Address List is not utilized, employees need to send signed emails to each other, allowing the sender to extract the recipient’s certificate. This limits effectiveness, as an encrypted email cannot be sent until the recipient replies to the email, working until the recipient renews their certificate and the sender now has an older, expired certificate. Once the source of the problem is identified, a new signed email must be sent to anyone the sender wishes to communicate with.
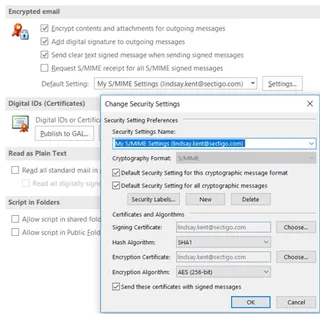
- Self-service web portal issues. Without automation, each employee requiring an S/MIME certificate must visit a self-service web portal. There, using a shared secret they identify themselves, they must click through 5-10 screens, download the private key and certificate in a PKCS#12 file, and open the file to import the certificate to their desktop. They then must manually configure Outlook to use the newly installed certificate.
- Ineffective private key storage. The employee will need to manually back up their private encryption key. This is so it can be used to continue to decrypt emails or files should the private key be accidentally destroyed. Two types of support issues can arise from this:
- The employee forgets to back up key and can no longer access their past emails when the private key is destroyed.
- The employee backs up the private key on a USB drive, mixed with other data files. Their private key can then be made available to an attacker, who can brute force the encryption protecting the private key from theft.
Some vendors claim to offer encryption key backup, but it requires the customer to implement it at their facility at an additional hidden cost.
- Mobile installation issues. Many employees struggle to export the private key and certificate from Outlook when setting up a mobile device. They need to transfer the file containing the private key and certificate to their mobile device. Employees will then need to import the private key and certificate to the mail application, which can prove troublesome due to the varied methods required for different mail applications. Once the private key and certificate are installed on the mobile device, many employees struggle to configure the mail application to use the newly installed certificate.
- Poor renewal management. When the certificate expires in 1-3 years, the employee will need to renew the certificate to each device prior to expiry. If not done, all email recipients will receive a notification that the digital signature is not valid, disrupting communications. Worse, the recipients ignore the errors from an expired certificate making the solution ineffective.
- Decrypting older emails. When certificates are renewed, emails stored on the mail server must be accessed using different keys. Without automation, employees must manually verify that the entire key history is available, or they will not be able to decrypt those older emails. This will lead to help desk calls—or worse, the inability to decrypt some emails associated with a lost key.
These issues can be frustrating for users, and clearly illustrate the ways in which ineffective certificate management can negatively impact both the security and reliability of an organization’s communications.
S/MIME is an important and easy-to-use email encryption tool, and the addition of our easy to deploy S/MIME will make the process of installing and renewing the many certificates in an organization simpler, and more cost-effective, than ever.