What Is Code Signing?
A code signing certificate is a digital certificate issued by a Certificate Authority (CA) that enables software developers to cryptographically sign applications, drivers, and executable files. It verifies the publisher’s identity and ensures the software has not been altered since it was signed. By confirming authenticity and integrity, code signing certificates eliminate security warnings from operating systems and browsers, build user trust, and protect software from tampering throughout distribution.
What Is Code Signing?
Code signing is a security process that uses PKI-based digital certificates to verify the identity of a software publisher and ensure that software has not been altered after it is released. By digitally signing applications, executables, and scripts, developers allow operating systems and users to confirm that software comes from a trusted source before installation or execution.
As part of the PKI framework, a trusted Certificate Authority (CA) validates the publisher’s identity and issues a code signing certificate. A digital signature is created by generating a cryptographic hash, or unique fingerprint, of the software and encrypting it with the publisher’s private key. When the software is downloaded or launched by a user, the corresponding public key in the certificate allows systems to verify that the publisher is authentic and that the code remains intact and unmodified.
What Is Code Signing Certificate?
A code signing certificate is a digital certificate issued by a CA that enables developers and organizations to digitally sign software as part of the code signing process. Based on X.509 certificate standards, it binds a verified publisher identity to a cryptographic key pair used to create and verify digital signatures.
Before issuing a certificate, the CA validates the identity of the software publisher or organization. Once issued, the certificate allows developers to sign applications, executables, scripts, and software updates so operating systems can verify both the origin of the software and its integrity.
Applications signed with trusted code signing certificates help reduce security warnings, improve user confidence, and protect against malware distribution and software supply-chain tampering.
How code signing works
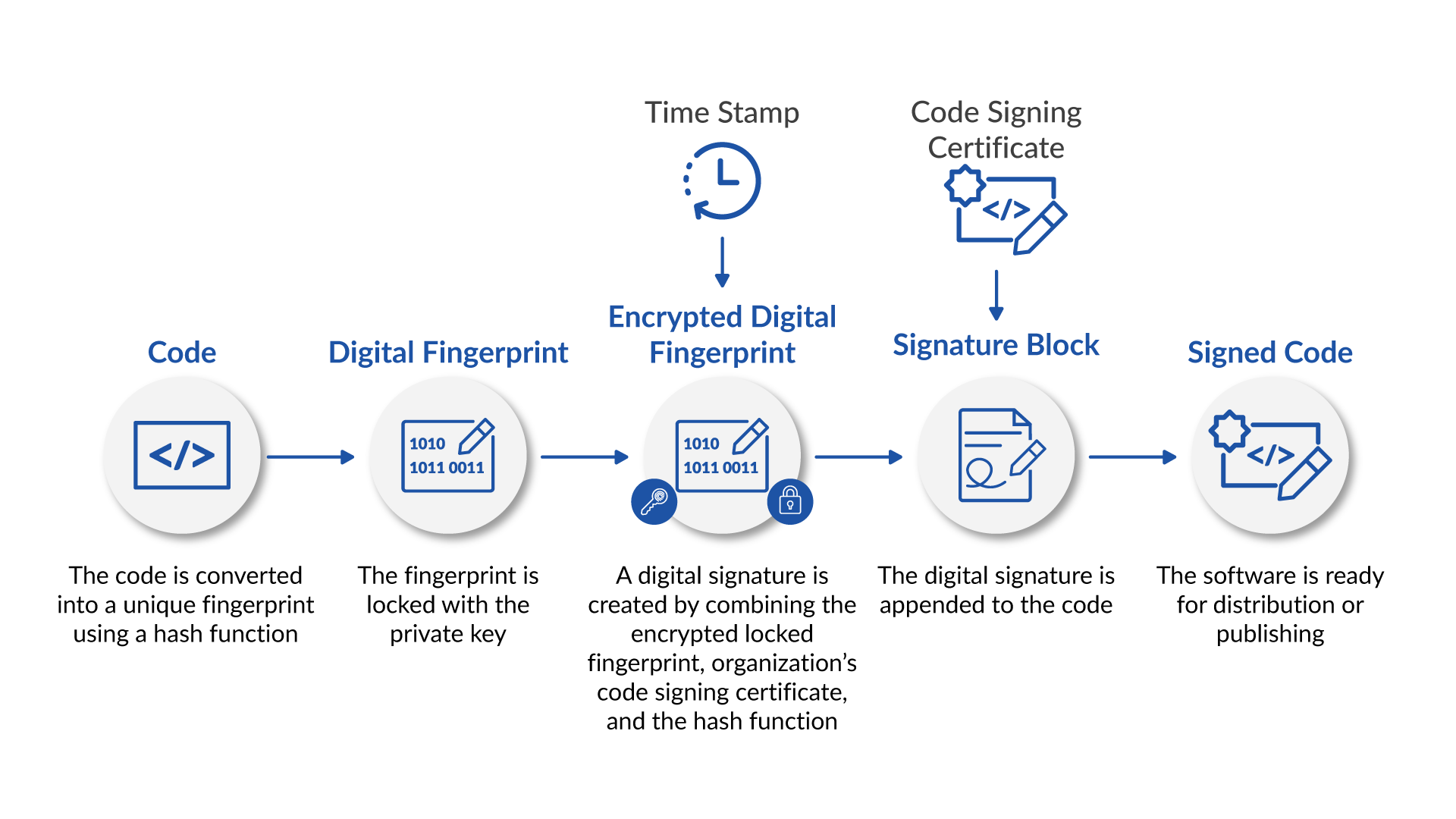
The code signing process follows a series of steps that transform software into a securely signed and verifiable software package:
- Code is converted into a digital fingerprint - Before distribution, a cryptographic hash function is applied to the software to generate a unique digital fingerprint. This fingerprint represents the exact contents of the software package at the time of signing.
- The fingerprint is encrypted using the publisher’s private key - The developer encrypts the fingerprint with their private key, creating an encrypted digital fingerprint.
- A timestamp is applied during signing - A trusted timestamp records when the software was signed. It allows the signature to remain valid even if the code signing certificate later expires.
- A signature block is created - The encrypted fingerprint is combined with the organization’s code signing certificate and the hashing information used during signing. Together, these components form the digital signature, often referred to as a signature block.
- The digital signature is appended to the software - The signature block is attached directly to the application or executable file, preparing the software for secure publishing or distribution.
- Operating systems verify the signed software - When the software is downloaded or installed, the operating system checks the digital signature to confirm it comes from a verified publisher and has not been tampered with. If the signature cannot be trusted, warnings may appear or installation may be blocked.
Different types of certificates
There are two primary categories of code signing certificates, both of which are offered by Sectigo:
- A standard certificate requires basic validation of the requester and their organization by the issuing Certificate Authority. Keys are usually stored in software or the filesystem, providing a foundational level of protection suitable for many software distribution needs.
- An Extended Validation (EV) Code Signing Certificate requires a more in-depth vetting process by the CA before issuance. The stricter requirements are designed to discourage fraudulent organizations from attempting to obtain an EV certificate. To further protect against misuse, EV signing keys must be stored in secure hardware environments. EV code signing certificates follow security principles similar to EV SSL/TLS certificates. Research from Georgia Tech’s Cyber Forensics Innovation Lab shows that the issuance and use of EV SSL certificates make it 99.99% likely to be free of phishing attacks and abuse. The research study, which was sponsored by Sectigo, can be downloaded here.
Why is code signing important?
Modern operating systems verify software before allowing installation or execution. If the software is unsigned or issued by an untrusted publisher, the user may see security warnings indicating that it cannot be verified. While installation may still be possible in some cases, these warnings often reduce user confidence and lead to abandoned downloads.
Code signing certificates help prevent this issue by allowing operating systems to confirm that software comes from a verified publisher and has not been modified since it was released. This establishes trust between developers and end users while helping organizations improve installation rates and protect their reputation.
Code signing also plays an important role in protecting software throughout the development and release process. Organizations commonly safeguard signing keys using secure vaults or Hardware Security Modules (HSMs), helping prevent unauthorized access and reducing the risk of compromised builds or malicious code injection.
Use cases
Code signing is widely used to protect software distribution across modern platforms. Operating systems and application marketplaces rely on digital signatures to verify that updates and downloadable applications come from legitimate publishers and have not been altered after release.
This is especially important in environments where users may not directly approve installations, including IoT devices, embedded systems, and smart technologies that receive automatic software updates. In these cases, code signing helps ensure that only trusted software can be installed or executed.
Code signing in DevOps environments
Code signing also plays an important role in modern software development pipelines. Developers digitally sign software before distribution, allowing end users downloading signed 32-bit or 64-bit programs to confirm the code comes from the developer and has not been modified since signing.
As release cycles accelerate, manual validation steps, hardware requirements, and disconnected signing workflows can slow deployments and introduce friction into development pipelines. Modern DevOps environments require code signing processes that integrate directly into automated build and release workflows without delaying software delivery.
To support this shift, certificate lifecycle management and signing processes increasingly integrate with automation standards such as Automated Certificate Management Environment (ACME) to reduce operational overhead. Platforms such as Sectigo Certificate Manager help organizations incorporate secure code signing into DevOps workflows across tools commonly used in modern infrastructure, including Kubernetes, Chef, Ansible, Salt Stack, Terraform, Puppet, Istio, and Docker. This allows development teams to maintain strong software integrity protections while keeping releases fast and scalable.
Do developers need to use code signing certificates?
In short, yes. Code signing certificates are an integral part of ensuring the integrity of software across all popular programming environments. Development organizations that fail to use them often find their users encountering operating system errors and security warnings, resulting in a poor user experience at best and complete distrust of the application at worst.
Deliver trusted software with code signing
Code signing helps organizations protect software integrity, reduce operating system security warnings, and ensure applications are recognized as coming from a verified publisher.
With Sectigo Code Signing Certificates, teams can improve install trust, streamline signing workflows, and protect every build from unauthorized tampering while keeping releases fast and user confidence high.