Issue and Manage Both Publicly-Trusted and Private Certificates in HashiCorp Vault with Sectigo Vault PKI Plugin


HashiCorp Vault provides a streamlined workflow that authenticates and encrypts containers and data using private certificates generated by Vault’s native PKI engine and a self-signed root certificate authority (CA). DevOps teams are now facing the same challenges they faced in order to get publicly-trusted certificates in an easy and efficient manner. Thankfully, Sectigo can help.

HashiCorp Vault provides a streamlined workflow that authenticates and encrypts containers and data using private certificates generated by Vault’s native PKI engine and a self-signed root certificate authority (CA). If you ask your DevOps team, they’ll simply say Vault makes it easy to generate and store SSL/TLS certificates on demand. And before Vault, that process was cumbersome and rife with workarounds and rogue certificates that exposed their applications to risk.
Unfortunately, these private certificates aren’t trusted by the most popular browsers when external-facing applications are deployed into production. Furthermore, your InfoSec team has difficulty enforcing corporate security policy and maintaining visibility of private certificates issued by the built-in CA.
So, DevOps teams are now back to the same challenges they faced in order to get publicly-trusted certificates. They often don’t have an automated way of getting certificates from public CAs, and they’re forced to wait while their InfoSec team provisions a public certificate. Some may use their own workarounds which can cause compliance issues with your organization’s security policies and regulatory frameworks.
With Sectigo Certificate Manager (SCM), DevOps teams need a seamless way to leverage the benefits of HashiCorp Vault without risking enterprise security requirements.
Extending Vault Using Sectigo Certificate Manager
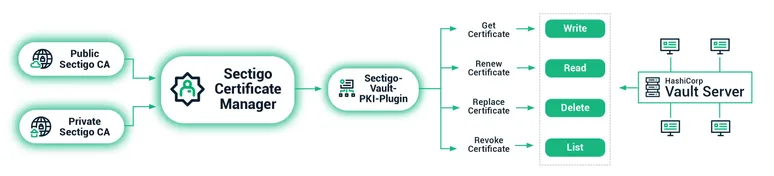
DevOps teams can leverage Sectigo to easily request and issue both publicly-trusted and private certificates using the Vault processes they use every day, including container certificates and code signing certificates. The Sectigo HashiCorp Vault integration provides a seamless solution for the enrollment, collection, revocation, renewal, and replacement of public SSL and private container authentication certificates issued by Sectigo Certificate Manager (SCM). This integration is distributed as a custom plugin for Vault built and maintained by Sectigo. Contact Sectigo for access.
Plus with the Sectigo HashiCorp Vault PKI plugin, your DevOps team can incorporate compliant certificate processes into their normal workflow while InfoSec gets the visibility and an easily auditable solution that they need. By connecting to Sectigo Certificate Manager for automated certificate lifecycle management, it’s easier to diagnose problems and prevent outages that can easily occur when managing a large quantity of short lifetime container certificates deployed throughout your environment. And unlike some solutions that enforce certificate policies after certificates are installed, the Sectigo Vault PKI plugin ensures the certificates comply with the policy configured by your DevSecOps before issuance. So, you have peace of mind that you are always issuing a compliant certificate and won’t have to burn cycles tracking down non-compliant certificates.
Issue and Manage Private CA Certificates with a Single Pane of Glass
In addition to deploying publicly-trusted certificates, you can also issue and manage private CA certificates using the same Vault PKI plugin integration with Sectigo Certificate Manager. Whether you are using HashiCorp private certificates, Sectigo Private CA, or your own existing private root CA certificates, Sectigo Certificate Manager offers you a single pane of glass management platform that automates the end-to-end lifecycle of public and private certificates. Now you issue and manage container certificates, sign your code, and deploy all the types of certificates you use from one dashboard -- at the scale and speed you need for your DevOps environment.
Not only does Sectigo Certificate Manager centrally enable interoperability, high uptime, and governance, it is also functionally capable of improving administration and certificate lifecycle management through:
• Automation: Completing individual tasks while minimizing manual processes.
• Coordination: Using automation to manage a broad portfolio of certificate administration tasks.
• Scalability: Managing certificates numbering in the hundreds, thousands, or even millions.
• Crypto-agility: Updating cryptographic strength and revoking and replacing any at-risk certificates rapidly in response to new or changing threats.
• Visibility: Viewing certificate status with a single pane of glass across all use cases.
Better yet, if you need to stand up a new Private CA, Sectigo Private CA and Sectigo Certificate Manager make it easy. You can set up your Private CA and its topology instantly through a simple to use UI.
How Sectigo Vault PKI Plugin Works
The Sectigo Vault PKI plugin supports both the generation and storage of new SSL and client certificates in HashiCorp Vault and (optionally) automates the renewal of certificates that fall within a certificate expiry window that you can specify. Based on your Sectigo account setup, there are various types of SSL and client certificates that can be requested by supplying the appropriate configuration options.
The Sectigo Vault PKI plugin provides the following features:
• RSA 2048, 3072, and 4096-bit private key and CSR generation
• Certificate Signing Request (CSR) enrollment and management of public and private certificates
• Storage and state tracking of certificates issued by Sectigo Certificate Manager in HashiCorp Vault
The workflow to enroll and manage certificates on Vault through Sectigo Certificate Manager is straightforward and will be familiar to Vault users. There are four primary steps:
1. configuring the plugin directory
2. setting up environmental variables
3. enabling the plugin
4. And then interacting with the plugin to enroll, read, revoke, replace, and renew certificates
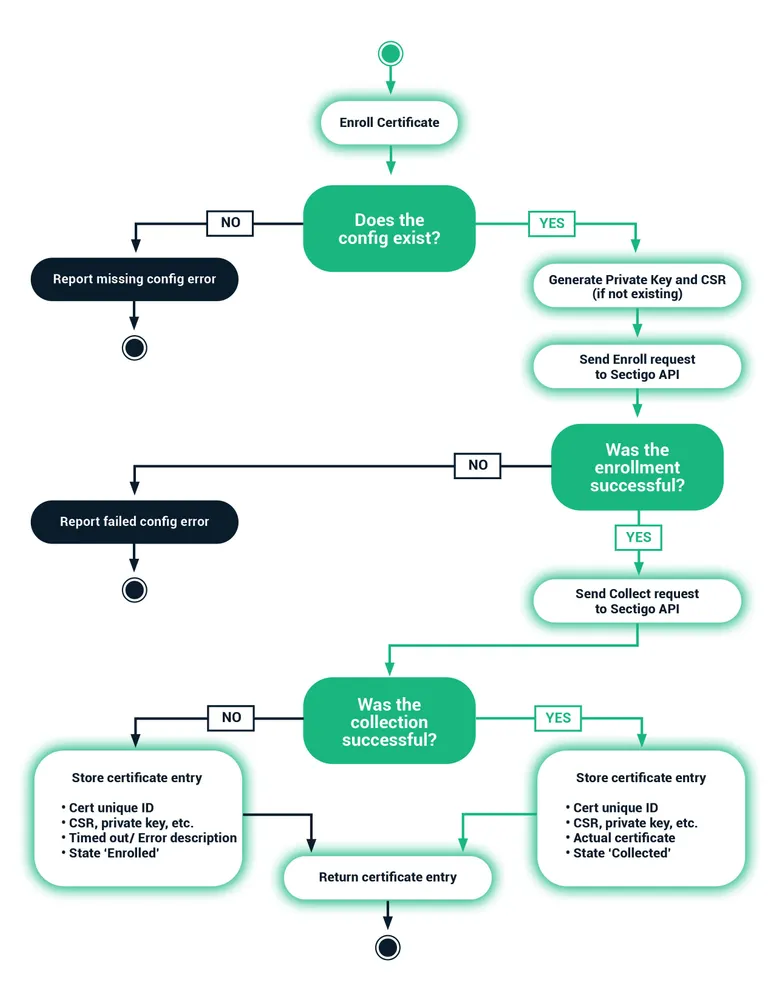
The following diagram illustrates a typical certificate enrollment workflow using the Sectigo HashiCorp Vault PKI plugin:
Users may interact with Vault directly through the Vault CLI tool, or they may interact with the exposed API endpoints through a tool such a cURL. The Sectigo Vault PKI plugin can handle a multitude of parameters, including configuration and user-specific parameters, CSR parameters, and certificate issuance and collection parameters. The required parameters depend on your applicable use case and are either passed to Vault bundled in a JSON file through a Vault CLI tool or through cURL commands or passed individually as key/value pairs when interacting with Vault through the Vault CLI tool.
Learn More
With Sectigo Vault PKI plugin, your DevOps team gets programmatic issuance and management of both private and publicly-trusted certificates for containers and code signing using Vault as they usually do, and your InfoSec team gets the visibility needed to enforce certificate policies and remain compliant.
To learn more, read the Sectigo-HashiCorp Vault Integration Guide or email the Sectigo DevOps onboarding team to get the Sectigo Vault PKI plugin and a free trial of Sectigo Certificate Manager.
About Sectigo
Sectigo is a leading cybersecurity provider of digital identity solutions, including TLS/SSL certificates, DevOps, IoT, enterprise-grade PKI management, and multi-layered web security. Recognized for its award-winning innovation and best-in-class global customer support, Sectigo has the proven performance needed to secure today’s digital landscape. As more and more companies are adopting DevOps to shrink development cycles and improve the quality and functionality of their products, engineering teams don’t want to spend their time on certificate management or cybersecurity policy enforcement. With Sectigo PKI solutions, you can automatically provision public and private SSL certificates to ensure the identity and integrity of containers, the code that they run and the production applications that use them. Sectigo Certificate Manager can interoperate with popular DevOps tools and environments through its RESTful API and the industry standard ACME.